Hyperbridge, a decentralized bridge connecting the Polkadot ecosystem to the Ethereum network, suffered a major security breach that allowed an attacker to mint 1 billion unauthorized DOT tokens.
However, the hacker’s potential multimillion-dollar payday was drastically cut short to around $240,000 as there simply was not enough liquidity to cash out the fabricated assets.
While the direct financial losses from the exploit were relatively contained, the incident has sent shockwaves through the Polkadot ecosystem, driving the network’s DOT native token toward its all-time low amid broader market anxieties regarding cross-chain security.
Anatomy of the Hyperbridge exploit
Security experts explained that the vulnerability resided in how Hyperbridge’s contracts validated incoming cross-chain messages before passing them along to the token gateway.
Blockchain security firm BlockSec Phalcon identified the root cause as a “Merkle Mountain Range (MMR) proof replay vulnerability.” This is essentially a cryptographic blind spot that allowed the attacker to recycle old, valid security proofs and attach them to malicious, newly crafted requests.
At the core of the breach was a missing input validation within the system’s `VerifyProof()` function. In standard cross-chain operations, a bridge must verify that a request originating on one blockchain is authentic before executing a corresponding action, such as minting tokens, on another.
In this instance, the Hyperbridge contract failed to properly bind the submitted request payload to the validated proof. The system merely checked that a request hash had not been used before, without verifying if the proof actually matched the message it was supposed to authenticate.
By manipulating the index parameters, the attacker bypassed the system’s root computation entirely. This disconnect enabled the hacker to forge a valid cross-chain message, elevate their privileges to administrator status, and command the contract to mint 1 billion DOT tokens on Ethereum.
Meanwhile, the primary token minting was preceded by an initial, quieter attack. On-chain analyst Specter noted that roughly an hour before the massive DOT fabrication, an attacker exploited a related TokenGateway contract to siphon 245 ETH, worth approximately $537,000.
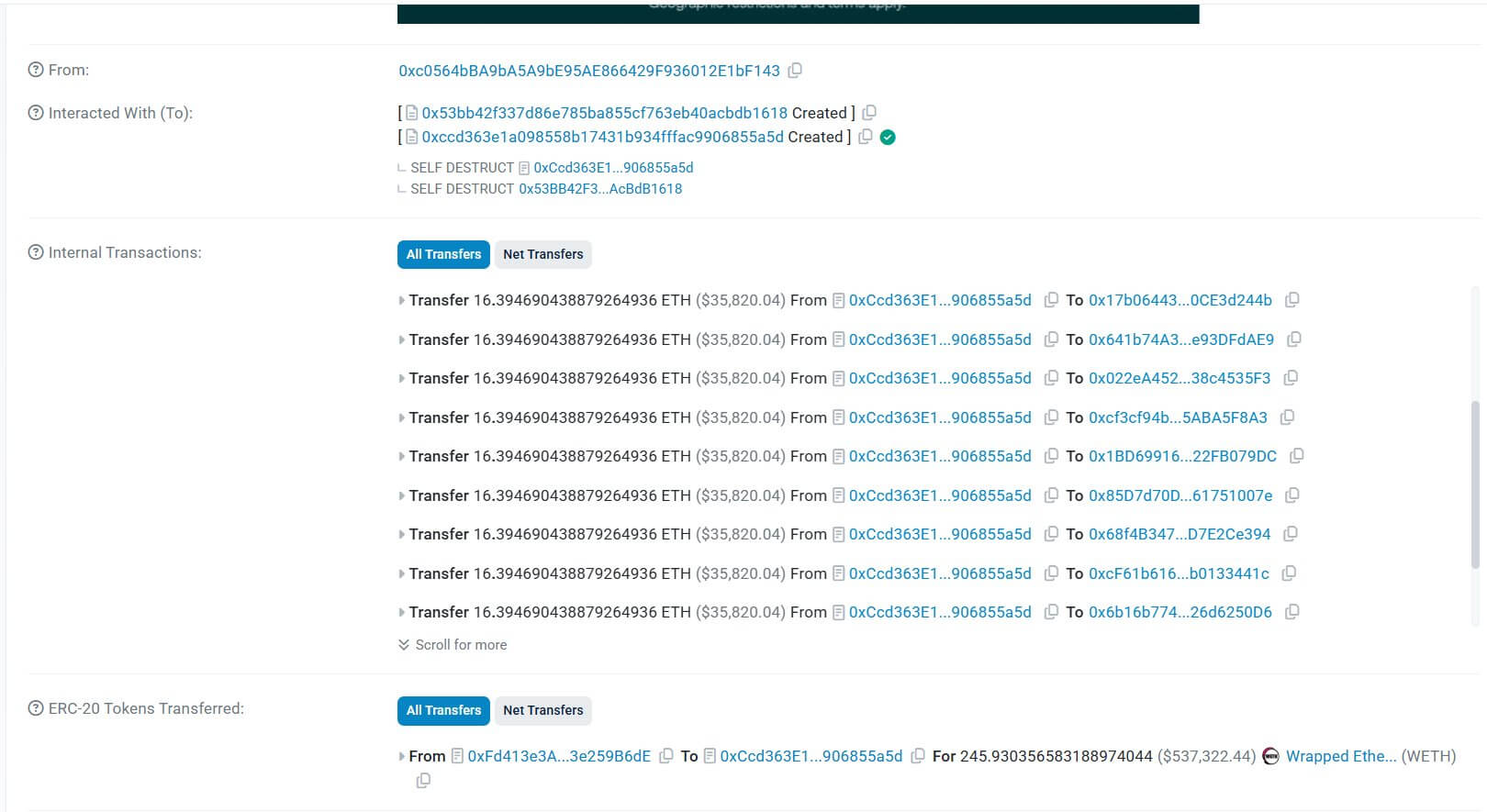
These funds were rapidly fragmented, distributed across 15 separate wallet addresses in increments of roughly 16.4 ETH, and laundered through the privacy protocol Tornado Cash.
How shallow market depth mitigated the damage
While the minting of 1 billion tokens usually signals a catastrophic, protocol-killing event, the attacker was thwarted by the very mechanics of decentralized finance: market depth.
When a hacker steals assets, they typically swap them into an automated market maker (AMM) liquidity pool for a more liquid, stable asset, such as Ethereum or a stablecoin. A liquidity pool prices assets based on the ratio of tokens held within it.
In this scenario, the bridged DOT pool on Ethereum was relatively shallow. When the attacker attempted to dump 1 billion forged tokens into the pool to extract ETH, the sheer volume of the sell order immediately overwhelmed the available liquidity.
As a result, the algorithm, rebalancing the ratio, drastically reduced the price of bridged DOT from $1.22 to tiny fractions of a cent within milliseconds.
Because the market could not absorb the massive order at stable prices, the attacker’s profit was severely capped.
Blockchain analytics firm Arkham Intelligence reported that the hacker was only able to extract roughly $240,000 worth of ETH from the DOT liquidity pool.
Meanwhile, had the vulnerability been exploited in a deeper pool or with a higher-value bridged asset, the financial devastation would have been exponentially greater.
From April Fools’ prank to reality
Meanwhile, this recent breach carries a heavy dose of irony for the Hyperbridge development team, arriving less than two weeks after the project published an April Fools’ Day joke about suffering a catastrophic exploit.
On April 1, Hyperbridge’s official channels posted a fake incident report claiming a $37 million breach across its Ethereum, Arbitrum, and Base deployments.
The mock post blamed fictional North Korean Lazarus Group hackers, rogue artificial intelligence agents, and even quantum computing. The post went so far as to joke that external auditors had attempted to warn the team, but developers were offline, eating KitKat bars to celebrate an engineer becoming a father.
At the time, the project brushed off community criticism of the joke, publicly boasting that their core community knew the protocol was “un-hackable.”
That hubris has evaporated as of press time, as the protocol developers were forced to halt the platform in real time.
Parity Technologies, the primary development firm behind the Polkadot ecosystem, quickly stepped in to manage the fallout. The firm clarified that the exploit was strictly isolated to Hyperbridge’s Ethereum gateway contract.
It added that Polkadot’s core network, its connected parachains, and native DOT tokens remained fully secure and untouched by the breach.
Contagion fears push Polkadot toward all-time lows
Even though the underlying Polkadot blockchain was never compromised, the psychological impact of its most dominant bridge being exploited has taken a heavy toll on its native currency.
Following the news of the breach, Data from CryptoSlate showed that Polkadot’s native DOT token fell 5% during early Asian trading hours on Monday, dropping to $1.14.
The decline pushes the asset perilously close to its all-time low of $1.13. The token has been locked in a brutal downward spiral, shedding roughly 70% of its value over the past year amid a broader crypto market downturn and waning retail interest in legacy alternative layer-one networks.
For the Polkadot ecosystem, the Hyperbridge exploit is a worst-case scenario regarding market optics.
Even as developers emphasize the technical distinction between a vulnerable third-party Ethereum contract and the secure core Polkadot network, retail investors often view the brand as a monolith.
Until cross-chain infrastructure can achieve the same level of security as the underlying blockchains it connects to, these liquidity events will continue to drag down the broader market’s confidence.
Bridges remain Web3’s weakest link
Meanwhile, the Hyperbridge incident underlines a persistent and systemic vulnerability in decentralized finance: cross-chain bridges are inherently fragile.
In the Web3 ecosystem, bridges are essential infrastructure. They allow disparate, siloed blockchains to communicate, offering users greater flexibility, lower fees, and access to a wider array of decentralized applications.
However, to function, these bridges must hold massive reserves of locked assets on one side to issue corresponding “wrapped” assets on the other.
Because these protocols essentially act as massive honeypots governed by complex smart contracts, they represent the single most lucrative target for cybercriminals.
If a hacker can compromise the private keys of the bridge’s validators or, as in the Hyperbridge case, exploit a vulnerability in the smart contract’s code, they can seize administrative control and drain the underlying assets or print infinite supply.
Notably, the history of crypto is littered with devastating bridge exploits. In March 2022, the Ronin Network bridge, built for the Axie Infinity gaming ecosystem, was drained of over $600 million in one of the largest heists in crypto history.
Later that year, the BNB Chain’s cross-chain bridge suffered a code exploit, resulting in the unauthorized creation of 2 million BNB tokens worth roughly $566 million. Other catastrophic breaches include the $321 million Wormhole hack and the $190 million Nomad bridge exploit.


