Search
Copyright © 2023 CryptoKeeperCanada. All Rights Reserved.
AI News
Meet ‘North Mini Code’: Cohere’s 30B Open-Weight Mixture-of-Experts Model With 3B Active Parameters for Agentic Coding
This week, Cohere AI team shipped its first developer-facing coding model named ‘North Mini Code‘. ‘North Mini Code’ is open-weight and focused at software engineers.…

Grow, expand and leverage your business..
Foxiz has the most detailed features that will help bring more visitors and increase your site’s overall.
Google AI Releases DiffusionGemma, a 26B MoE Open Model Using Text Diffusion for Up to 4x Faster Generation
Google AI team including the Google DeepMind researchers have just released DiffusionGemma,…
How to Refactor Code with Claude Code
are amazing at quickly implementing a lot of code. However, if you’ve…
Introducing DiffusionGemma
Why diffusion for text?While the AI research community has explored diffusion-based text…
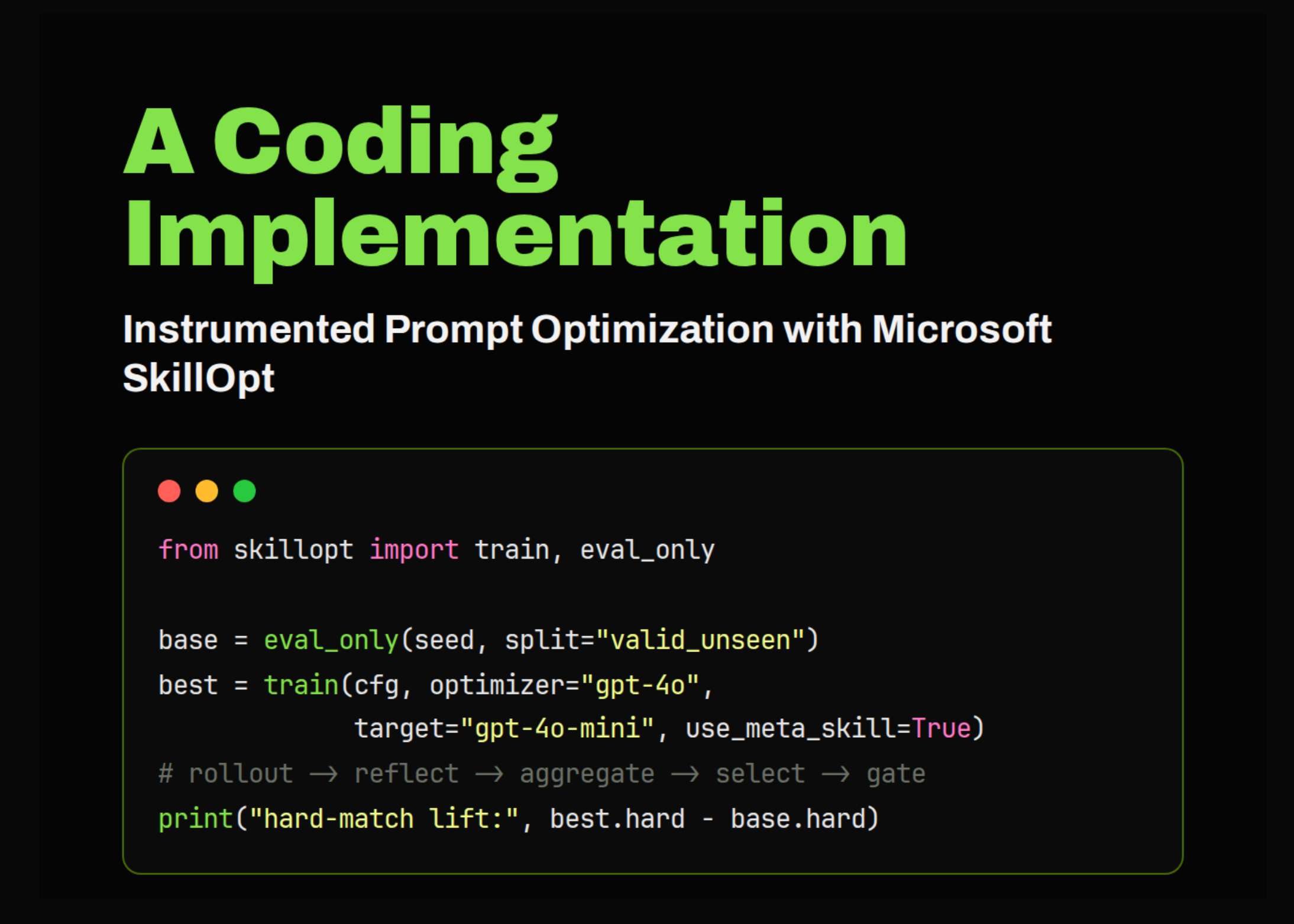
How to Train a Scoring Model in the Age of Artificial Intelligence
All code used in this section is available on GitHub. The business…
Bayesian Networks and Markov Networks: An Intuitive Guide to Structured Uncertainty
explanations begin with prediction. A churn model estimates whether a customer is…
Physical AI: What It Is and What It Is Not
Physical AI is the . NVIDIA is talking about it, consulting firms…
Top AI Coding Agents and Development Platforms in 2026: Atoms, Devin, Windsurf, Cursor, Warp, and More Compared
Development has shifted from typing code by hand to describing intent and…